by Cyber Protect Staff | May 1, 2026 | CYBER RISK INTELLIGENCE SERIES
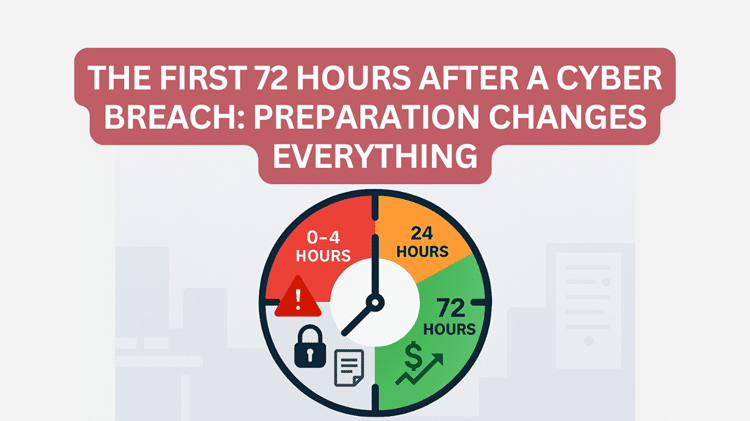
Article 3 of 5 Applied to Three Real Michigan SMB Profiles Risk Modeling Tells You the Odds. Preparation Determines the Outcome. The first two articles in this series focused on measuring risk. Using Laplace’s Rule of Succession, Beta Distribution modeling,...

by Cyber Protect Staff | Apr 24, 2026 | CYBER RISK INTELLIGENCE SERIES
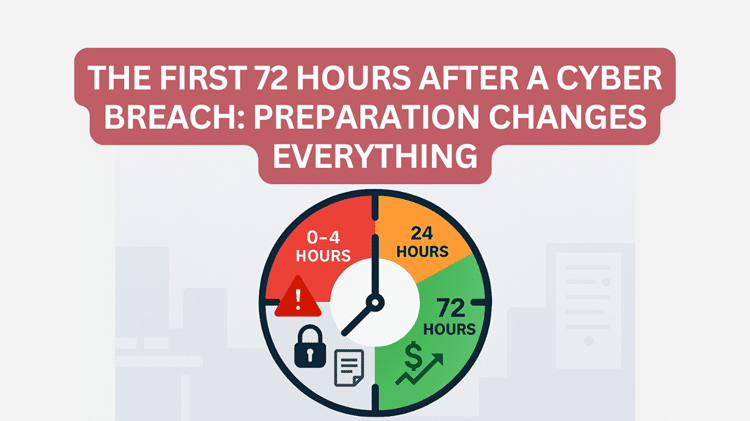
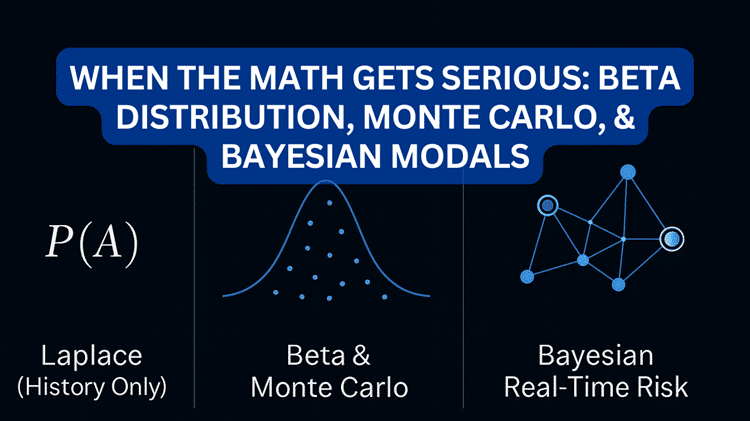
Article 2 of 5 Applied to Three Real Michigan SMB Profiles From Starter Math to Professional Risk Intelligence In our companion article, we introduced Laplace’s Rule of Succession as an accessible entry-level tool for quantifying cyber risk. We showed that even...

by Cyber Protect Staff | Apr 17, 2026 | CYBER RISK INTELLIGENCE SERIES
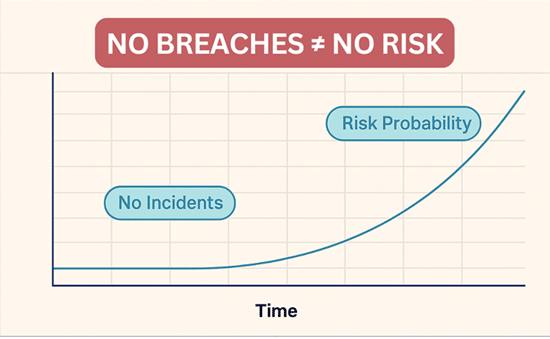
Article 1 of 5 Why “Nothing Has Happened Yet” Is Not a Security Strategy Every week, business owners across Michigan sit in boardrooms and budget meetings and say some version of the same thing: “We’ve been operating for eighteen years and never had a major breach....

by Cyber Protect Staff | Mar 20, 2026 | General
The recent Stryker network disruption is a strong reminder that a Microsoft compromise can hurt operations even when there is no public sign of ransomware. In its March 11 and March 12, 2026 updates, Stryker said it was dealing with a cyberattack that caused a global...

by Cyber Protect Staff | Mar 12, 2026 | General
There’s no shortage of people willing to sell your business a cybersecurity product — antivirus software, VPNs, password managers, and everything in between. The industry generates billions of dollars a year selling tools to businesses just like yours. But here’s the...