Blog
Shielding Your Data from Cyber Threats.Cyber Risk by the Numbers
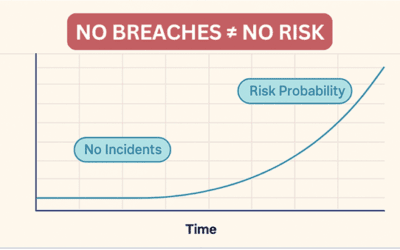
Article 1 of 5 Why “Nothing Has Happened Yet” Is Not a Security Strategy Every week, business owners across Michigan sit in boardrooms and budget meetings and say some version of the same thing: “We’ve been operating for eighteen years and never had a major breach....
7 Critical Lessons from the Stryker Microsoft Cyber Incident
The recent Stryker network disruption is a strong reminder that a Microsoft compromise can hurt operations even when there is no public sign of ransomware. In its March 11 and March 12, 2026 updates, Stryker said it was dealing with a cyberattack that caused a global...
Small Business Cybersecurity: 10 Truths You’re Not Hearing (2026 Guide)
There’s no shortage of people willing to sell your business a cybersecurity product — antivirus software, VPNs, password managers, and everything in between. The industry generates billions of dollars a year selling tools to businesses just like yours. But here’s the...
Turn On Enhanced Protection in Chrome & Edge to Stop Phishing Attacks
A Fast Win Against Phishing Most businesses don’t get hacked because of some Hollywood‑style break‑in. They get hacked because someone clicks a link that looks legitimate. Modern phishing sites are polished, convincing, and often hosted on trustworthy‑looking...
Turn On Windows 11 System Restore: A Simple Way to Prevent Costly Downtime
If something breaks on your PC, after a bad update, a driver install, or even a suspicious program, most firm owners don’t realize how quickly a “small issue” can become lost time, missed deadlines, and costly downtime. Windows 11 System Restore is a built-in safety...
Stop Using Admin Accounts for Daily Work: The #1 Windows 11 Security Fix for Small Businesses
Why Everyday Admin Logins Put Your Firm at Risk Most security incidents don’t start with advanced hacking. They start with a simple mistake—clicking the wrong link, opening the wrong attachment, or running a fake update. When you use an administrator account...
Protecting Your Business in 2026 Using CTEM
You’re a business owner, you’ve probably said or thought at least one of these: “We’re too small to be a target.” “We don’t have anything hackers would want.” “I’m not a tech person; this stuff is overwhelming.” That mindset used to feel reasonable. In 2026, it’s...
Why Built-In Spam Filters Fail: Essential Email Security Tips for SMBs
Email remains the primary route attackers use to compromise businesses. If you assume your built-in spam or email filtering system takes care of the risk, you may be dangerously mistaken. Recent industry data shows that threat actors are systematically bypassing...
Top Cybersecurity Threats Facing Michigan Law Firms
Law firms across Michigan are increasingly targeted by cybercriminals. Why? Because legal practices hold a goldmine of sensitive data—client records, financials, case files, and confidential communications. A single breach can jeopardize attorney-client privilege,...
How to Stop Phishing Emails with the SLAM Method
How to Stop Phishing Emails with the SLAM MethodPhishing attacks are constantly evolving—and so must your defenses. While email filters from providers like Barracuda or Mimecast catch many threats, no system is foolproof. That’s why human vigilance remains your last...
Is Your Microsoft 365 Really Secure?
Why Default Settings Leave You Vulnerable—and What You Should Do About ItMicrosoft 365 (M365) is the engine behind today’s digital workplace, offering powerful tools like Outlook, Teams, Word, and OneDrive. But here’s the reality many businesses overlook: M365 is not...
Perplexity Comet Browser: AI Innovation or Data Privacy Risk?
In the rapidly evolving landscape of artificial intelligence, new tools are emerging that promise to redefine our digital workflows. Among these innovations is Perplexity Comet, an "agentic AI-powered browser built on Chromium". Marketed as a tool to "boost your...
The Shadow Threat in AI
The Illusion of SafetyArtificial Intelligence feels like magic—until it isn’t. Nowadays, business owners and executives are eager to connect AI tools to everything: email, workflows, and support systems. The potential for efficiency is real, but so is the risk. The...
Why Relying on a Single Cybersecurity Vendor Leaves Your Business Exposed
The Illusion of SafetyMany business owners feel safer when they place their trust entirely in one major cybersecurity vendor. The promise sounds appealing: one dashboard, one contract, one provider. But the reality is that vendor lock-in creates blind spots, weakens...
The Importance of Cybersecurity for Law Firms
Protecting client confidences isn't just a best practice for lawyers; it's a fundamental ethical and legal obligation. Yet, in the face of increasingly sophisticated cyberattacks, many law firms struggle to keep pace. The consequences of a data breach can be...
Inside a Ransomware Attack: How One Business Lost Everything Overnight
It began like any other workday—until it wasn't. When employees at a Midwestern business arrived at 8:00 a.m., they were met with frozen screens, strange popups, and locked files. By the time their internal IT team called us, the damage was done. The ransomware attack...
Why Business-Class PCs Are Essential for Your Company
Don’t Let Consumer-Grade Hardware Put Your Business at RiskIf you’re running your business on the same kind of computer you’d buy at a big-box store for personal use, you could be setting yourself up for frustration—and risk. While consumer-grade systems are fine for...
The Ultimate Mobile Security App for Free
Protect Your iPhone or Android Device in Just a Few MinutesIn today’s digital world, our smartphones are more than just communication tools—they’re vaults for personal, financial, and business information. Whether you're checking your bank account, responding to work...
Cybersecurity at Home: A Beginner’s Guide to Securing Your PC from Hackers
This blog was inspired by a very real and important question posed during a recent conversation between Representative Viola Davis of Georgia and Cheyenne Harden of Cyber Protect LLC: “The average person with a home computer does not know what steps to take to protect...
How to Secure Mobile Devices in Law Firms: Best Practices for 2025
Mobile devices have become essential tools in modern law firms, enabling attorneys to work remotely and maintain constant communication with clients and colleagues. However, with this convenience comes an increased risk. Smartphones and tablets are now top targets for...
Beyond SSL: Why Modern Businesses Need Advanced Web Security Tools
The Era of "Free" Security Is Over – Here's What Business Owners Must KnowRemember when seeing that little green padlock in your browser meant a website was completely safe? Those days are gone. While SSL certificates once provided reliable security assurance, the...