Learning & Resource Center
Most Popular Posts
Cyber Breach Response: What the First 72 Hours Look Like
Article 3 of 5 Applied to Three Real Michigan SMB Profiles Risk Modeling Tells You the Odds. Preparation Determines the Outcome. The first two articles in this series...
Cyber Risk in Dollars: What a Data Breach Really Costs
Article 2 of 5Applied to Three Real Michigan SMB Profiles From Starter Math to Professional Risk Intelligence In our companion article, we introduced Laplace’s Rule of...
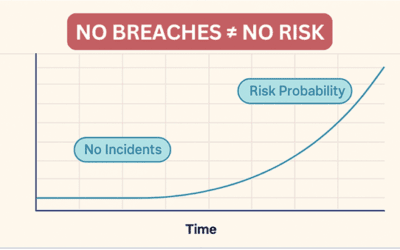
Cyber Risk Is Never Zero: What the Math Says About Breaches
Article 1 of 5 Why “Nothing Has Happened Yet” Is Not a Security Strategy Every week, business owners across Michigan sit in boardrooms and budget meetings and say some...
7 Critical Lessons from the Stryker Microsoft Cyber Incident
The recent Stryker network disruption is a strong reminder that a Microsoft compromise can hurt operations even when there is no public sign of ransomware. In its March 11...
Small Business Cybersecurity: 10 Truths You’re Not Hearing (2026 Guide)
There’s no shortage of people willing to sell your business a cybersecurity product — antivirus software, VPNs, password managers, and everything in between. The industry...
Turn On Enhanced Protection in Chrome & Edge to Stop Phishing Attacks
A Fast Win Against Phishing Most businesses don’t get hacked because of some Hollywood‑style break‑in. They get hacked because someone clicks a link that looks legitimate....
Tune In to Our Latest Videos





Stop Threats Before They Become Disasters
Cyber threats evolve fast. Don’t leave your business vulnerable to ransomware or zero-day attacks. Our EDR services ensure your endpoints are constantly monitored, secured, and ready to defend against the unexpected.
Get A Free Quote